The Benefits of Partnering with an IT Helpdesk
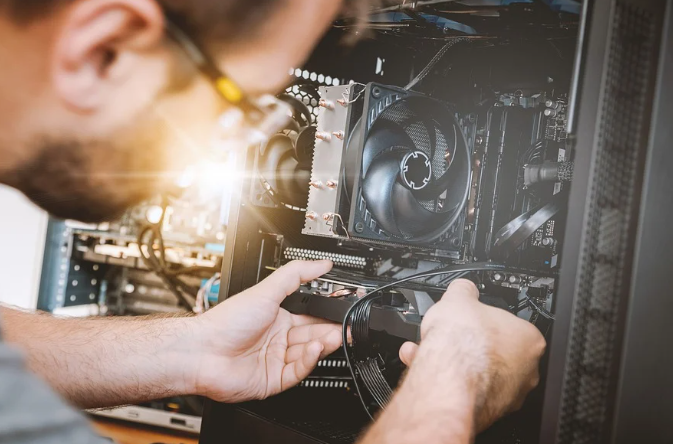
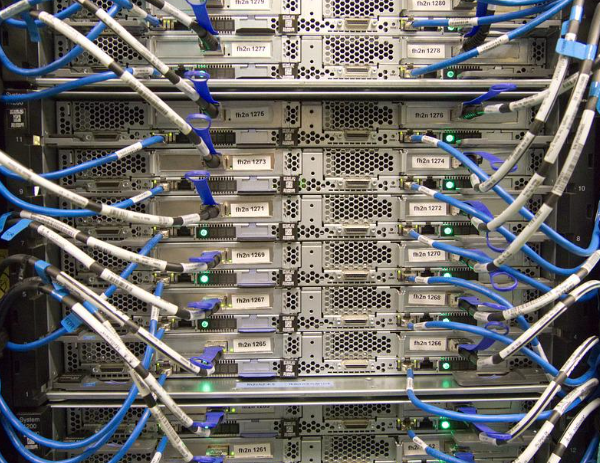
Almost all organizations rely on some form of IT infrastructure to run their operations. From managing financial records and customer information to service delivery, IT systems are the backbone of many day-to-day workflows. Because of this, a technical issue with your IT could result in major slowdowns to its productivity. For instance, an important deliverable…
Read more